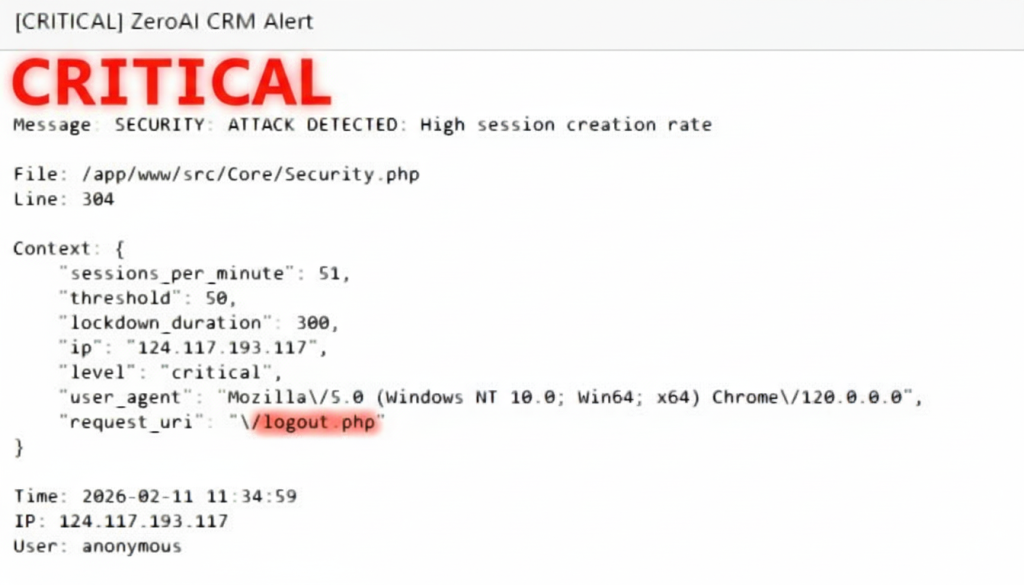
In the digital world, a split second is the difference between a secure perimeter and a total breach. The log entry above isn’t just data; it’s a snapshot of WebArmor and ZeroAI CRM working in perfect, automated harmony to stop a session-stuffing attack in its tracks.

The Anatomy of a Blocked Attack
At 11:34:59, an anomaly was detected. An IP address (124.117.193.117) attempted to generate 51 sessions per minute—just one over the safety threshold. Here is how the tag-team defense responded:
1. WebArmor: The Vigilant Gatekeeper
WebArmor functions at the core level of your application (specifically monitoring src/Core/Security.php). Its job is to watch the traffic flow with surgical precision.
- Threshold Monitoring: It identified that the traffic exceeded the 50-session limit.
- Instant Lockdown: Without needing human intervention, it triggered a 300-second lockdown for the offending IP.
- Contextual Awareness: It flagged the specific URI (
/logout.php), identifying a common tactic where attackers use logout loops to stress-test session managers.
2. ZeroAI CRM: The Intelligence Layer
While WebArmor handles the “muscle,” ZeroAI CRM provides the “brain.” By integrating security logs directly into the CRM, the system does more than just block; it learns.
- IP Reputation Tracking: ZeroAI logs the malicious IP and cross-references it against global threat databases.
- Behavioral Profiling: The CRM notes the User-Agent and request patterns to improve future detection, ensuring that “Mozilla/5.0” isn’t used as a mask for bot activity.
- Automated Reporting: A “Critical” alert is instantly generated for the admin, providing the full JSON context needed for a forensic audit.
Why This Integration Matters
Standard firewalls often work in a vacuum. By combining WebArmor’s deep-file protection with ZeroAI’s data-driven insights, you create a self-healing ecosystem.
- False Positive Reduction: ZeroAI analyzes if the “attacker” is a known customer or a malicious bot.
- Scalable Defense: As your traffic grows, your thresholds evolve automatically through ZeroAI’s machine-learning modules.
Conclusion
The “Security: Attack Detected” error isn’t a failure—it’s a success story. It proves that your infrastructure is watching, reacting, and documenting every threat before it can escalate.

